Haiku/New Haiku Information Discord
There is a sense of worry about not being able to get in contact, so please feel free to join this place for the interim. It is already organized.
https://discord.gg/upnZYFC
have a splatoon 2: octo expansion flipnote
While you wait, please enjoy this Splatoon Flipnote posted to Sudomemo!
I am developing a successor for Hatena Haiku
I am developing a successor for Hatena Haiku. It will be designed to be comfortable for Hatena users, and integrate into Hatena services as much as possible. I will post further details on this blog. I thank you for your patience.
うごくメモ帳10周年
うごメモはてなの十周年を記念して、
うごメモはてなは
Sudomemo(スドメモ) に生まれ変わりました。
このニュースを友達と共有して、
DSiからうごメモを投稿しよう!
(日本語翻訳ヘルパー募集中です)https://t.co/2ompFbZ2OM#うごくメモ帳10周年 #projectha10a #うごメモ #はてな #Sudomemo #スドメモ pic.twitter.com/YPJ3WcbKmZ
The Daily Draw is struggling...
I'm a bit disappointed about how the Sudomemo Daily Draw has somewhat faded so far.
I was hoping to bank on the nostalgia factor to attract old Hatena users from the days of Flipnote (うごメモ), but that doesn't seem to have worked too well.
I do seem to be receiving a number of new followers from Japan each day, though I have received no entries from the new subscribers. (Currently: 172 subscribers)
The concept seems pretty simple: a daily drawing prompt, meant to be done as a quick doodle. The winner gets a number of Hatena Stars, gets featured, and gets a Bookmark!
I think it might be popular if Hatena users were interested. I may need to change how I write the articles to indicate that it is indeed open to anyone at all with a Hatena account.
I'm going to keep going. I don't give up on things easily, since good things take hard work to accomplish.
Google is Scanning for (and Crawling) URLs in Your Private YouTube Videos
I was recently uploading an unlisted video to YouTube to demonstrate an XSS vulnerability I stumbled across which I was responsibly disclosing. Part of this involved showing the URL of the script which had been run. After uploading it to YouTube and submitting the vulnerability disclosure, I decided to double-check that nobody had visited the page I was testing on before I had removed the link. As it turns out, somebody had: YouTube.
66.249.90.79 - - [12/Dec/2018:14:23:40 -0500] "GET /js/redacted_1.js HTTP/1.1" 200 125 "-" "Mozilla/5.0 (compatible; Google-Youtube-Links)" 66.249.90.81 - - [12/Dec/2018:14:23:42 -0500] "GET /js/redacted_1.js HTTP/1.1" 200 125 "-" "Mozilla/5.0 (compatible; Google-Youtube-Links)" 66.249.90.79 - - [12/Dec/2018:15:24:21 -0500] "GET /redacted_subfolder/redacted_2.png HTTP/1.1" 200 4605 "-" "Mozilla/5.0 (compatible; Google-Youtube-Links)" 66.249.90.81 - - [12/Dec/2018:15:24:22 -0500] "GET /redacted_subfolder/redacted_3.png HTTP/1.1" 200 5102 "-" "Mozilla/5.0 (compatible; Google-Youtube-Links)" 66.249.90.79 - - [12/Dec/2018:15:24:23 -0500] "GET /js/redacted_4.js HTTP/1.1" 200 137 "-" "Mozilla/5.0 (compatible; Google-Youtube-Links)" 66.249.90.79 - - [12/Dec/2018:15:24:24 -0500] "GET /redacted_subfolder/redacted_2.png HTTP/1.1" 200 4605 "-" "Mozilla/5.0 (compatible; Google-Youtube-Links)" 66.249.90.79 - - [12/Dec/2018:15:24:26 -0500] "GET /redacted_subfolder/redacted_3.png HTTP/1.1" 200 5102 "-" "Mozilla/5.0 (compatible; Google-Youtube-Links)" 66.249.90.79 - - [12/Dec/2018:15:24:26 -0500] "GET /js/redacted_4.js HTTP/1.1" 200 137 "-" "Mozilla/5.0 (compatible; Google-Youtube-Links)"
I was rather alarmed to see this, as I didn't imagine the links were up long enough to be crawled by Google. It was then that I realized that during the video, those URLs were visible in the address bar. It seemed that YouTube had run OCR (optical character recognition) across my entire video and decided to crawl the links within. But how could I be sure that this was not just a mistake on my part?
Time for an Experiment
I recorded a new video of me accessing a URL that does not exist for the very first time.
Here is the video that I uploaded:
I started another screen recording of me uploading the video, and watching the access logs. A few minutes later, Google took the bait, and sent two requests to the URL:
66.249.90.81 - - [12/Dec/2018:18:42:02 -0500] "GET /nonexistent/url.js HTTP/1.1" 404 - "-" "Mozilla/5.0 (compatible; Google-Youtube-Links)" 66.249.90.79 - - [12/Dec/2018:18:42:04 -0500] "GET /nonexistent/url.js HTTP/1.1" 404 - "-" "Mozilla/5.0 (compatible; Google-Youtube-Links)"
Hook, line, and sinker! I recorded me uploading the video and watching my access logs live (the accesses are around the 5:50 mark):
Why is this concerning?

The purpose for which I uploaded the video was to report a vulnerability. I uploaded it unlisted, so far all intents and purposes, it was meant to remain private. However, our friend Google-Youtube-Links scanned it for an unknown purpose and sent several requests to that URL. A second test as a fully private (not just unlisted) video revealed the same result.
By uploading the videos as unlisted or private, I have the expectation that nobody will see the video or the contained within except for me, or for the people who I explicitly share the links with.
Let's propose a scenario which is in a similar realm to what I was doing:
A security researcher has found a critical vulnerability in a site, and has crafted a URL that will trigger it, causing harmful effects to the website. (e.g a SQL injection vulnerability that will drop the database tables).
During the video, s/he makes mention that they will not visit the URL as it would cause trouble, but it is displayed so that the company they are responsibly disclosing to can remedy it. They upload it as unlisted to YouTube and submit their report. Five minutes later, Google-Youtube-Links comes along and sends two requests to the URL, triggering the SQL injection and rendering the site broken.
The Illusion of Privacy
Here is Google's explanation of privacy settings:
What this does not include, however, is any mention that your video will be scanned for anything resembling URLs, and have these crawled.
What Google has to say about it
So what does Google have to say about this practice? Actually, nothing at all. Searching for the user-agent gives no relevant results save for one: a locked thread from a curious webmaster with no answer, back on March 27th, 2018. The thread was not resolved.
https://productforums.google.com/forum/?hl=en#!topic/webmasters/Ov_ODO8l2cU
This means that we are left with no explanation of why this is occuring, or disclosure that content uploaded as private to YouTube will be scanned with OCR and have any links within crawled by Google.
Honestly, I find this rather unsettling - especially for using private or unlisted YouTube videos as a way to quickly upload a video to disclose a vulnerability. I'm sure you can think of other scenarios in which this would be undesired, especially as we don't know why it's taking place or where those URLs will end up.
Let me know what you think of this development.
Questions or concerns?
If you have any questions or concerns, feel free to leave them below, or reach out to me at apburk@sudomemo.net. If you are a Hatena user, feel free to leave a star!
はてなハイクスパム対策
In English: Hatena Haiku Anti-Spam - austinburk's blog

はてなハイクスパム対策というサービスを開発しました。半年にわたる広範囲なテストにより、高い精度が実現されています。
背景
はてなにはスパムの問題があります。それも小さいものではありません。その影響ははてなが提供するほとんどのサービスに及び、特に目立つのは、ハイク、ブックマーク、ブログ、匿名ダイアリー、人力検索などです。フォトライフにもスパムの問題がありますが、私が調査しているものとは種類が異なります。
対策として、小規模な緩和策(ハイクなど一部のサービスの最初のエントリの障壁として人間性クイズを使用するなど)が試みられていますが、古いアカウントは適用の対象外となっています。これに関して、動作の一貫性が欠けているために、ユーザーが3回以上正解しても検証に成功しない場合があることを発見しました。
ハイクその他のサービスに投稿されるスパムは性質が非常に一貫しています。私は現在Webホスティング管理の会社に勤務し、ベイズフィルターと、Apache SpamAssassinという正規表現ベースのフィルタリングエンジンの組み合わせに関する経験があります。そこで、SpamAssassinにはてなハイクの投稿のフィルタリング機能を付け加え、より快適にサービスを使用できるようにしようと思い立ちました。
Eメールからのハイク
主に問題となったのは、SpamAssassinがEメールのフィルタリングに特化して設計されていること、つまり、Eメールメッセージのようなフォーマットの入力が想定されていることでした。
例(オリジナルの投稿):
Delivered-To: site@h.hatena.ne.jp
Received: by sudofox.spam.filter.lightni.ng (Sudofix)
id 81807923680507219; Fri, 08 Jun 2018 09:12:22 -0400 (EDT)
From: austinburk@h.hatena.ne.jp (Sudofox)
To: site@h.hatena.ne.jp
Subject: 食べた
Content-Type: text/plain; charset=UTF-8
Message-Id: <20180908091222.81807923680507219@sudofox.spam.filter.lightni.ng>
X-Hatena-Fan-Count:212
Date:Fri, 08 Jun 2018 09:12:22 -0400 (EDT)
食べた=That looks AMAZING QoQ
ヘッダーには、spamd (SpamAssassinのバックグラウンドで実行されるサービス)の解析の対象となる最小限の内容と、X-Hatena-Fan-Countが含まれています。
SpamAssassinのuser_prefsとカスタムルール
ここにuser_prefsファイルがあります。"Begin Sudofox config"の後をご覧になるとわかるとおり、Eメール関連のすべてのチェック(たとえばSPF、RBL、DKIM)を無効化するなどの変更をルールに加えて、ハイクからのメッセージのフィルタリングへの適合性を高めています。それ以外に、ハイクのプライマリユーザーベースにより適合させるための変更("Begin Sudofox config"の上にありますが注釈はしていません)も加えています。
また、ハイクに特有のSEOスパム(スポーツやテレビ番組の無料視聴に関連することが多い)に対処するために開発したルールもいくつかあります。
スパムユーザーにはファンがいないことがほとんどであるため、このことをメトリックとしてフィルタリングに使用できます。それがX-Hatena-Fan-Countの用途です。
header SUDO_HATENA_ZERO_FANS X-Hatena-Fan-Count =~ /^0$/
score SUDO_HATENA_ZERO_FANS 1.0
describe SUDO_HATENA_ZERO_FANS User has no fans
header SUDO_HATENA_FEW_FANS X-Hatena-Fan-Count =~ /^([1-9]{1})$/
score SUDO_HATENA_FEW_FANS -1.0
describe SUDO_HATENA_FEW_FANS User has 1-9 fans - spam less likely
header SUDO_HATENA_10_PLUS_FANS X-Hatena-Fan-Count =~ /^([0-9]{2})$/
score SUDO_HATENA_10_PLUS_FANS -2.0
describe SUDO_HATENA_10_PLUS_FANS User has 10-99 fans - spam unlikely
header SUDO_HATENA_100_PLUS_FANS X-Hatena-Fan-Count =~ /^([0-9]{3,})$/
score SUDO_HATENA_100_PLUS_FANS -10.0
describe SUDO_HATENA_100_PLUS_FANS User has 100+ fans - prob legitimate
スパムの作成者が私のブログの投稿を読んで適応したとしても、実際のスパムのコンテンツのスコアは通常は高いため、互いをファンとして追加することで2ポイントがマイナスされてもなお、スパムとして認識できると考えています。
ソースコードはこちらです。実験的に開始したため、若干未整理です。しかし、はてなユーザーが実際に(APIやユーザースクリプト経由で)使用するサービスに成長したため、近いうちに全体を書き直す予定です。
このリポジトリには、スパム分類コードとspamdに関連する内容のみが含まれています。
Webサイト
はてなハイクスパム対策には、ブラウズできる2つのセクションとして、メインの概要ページとユーザー情報ページがあります。

メインページには2つの円グラフがあり、左のものは最近のスパムユーザーを示し、右のものは最近の正当な投稿を示します。表示対象の期間は24時間で、円グラフの任意のスライスをクリックすると、ユーザー情報ページが表示されます。
ユーザー情報ページには、そのユーザーの全体的なスコアのグラフが以下のように表示されます。
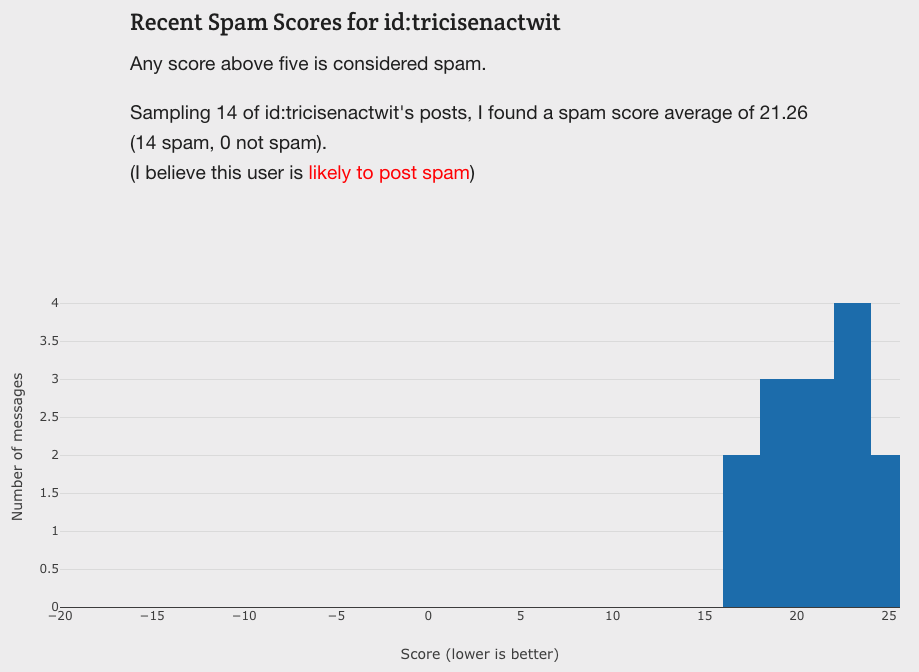
また、ここには、10投稿のサンプルと、それらがどのように分類されているかが示されます。実際のスパムコンテンツを再びパブリッシュすることがないよう、採取したテキストのサンプルはbase64エンコードのスニペットとして保存し、HTMLキャンバスにレンダリングすることで表示できるようにしています。
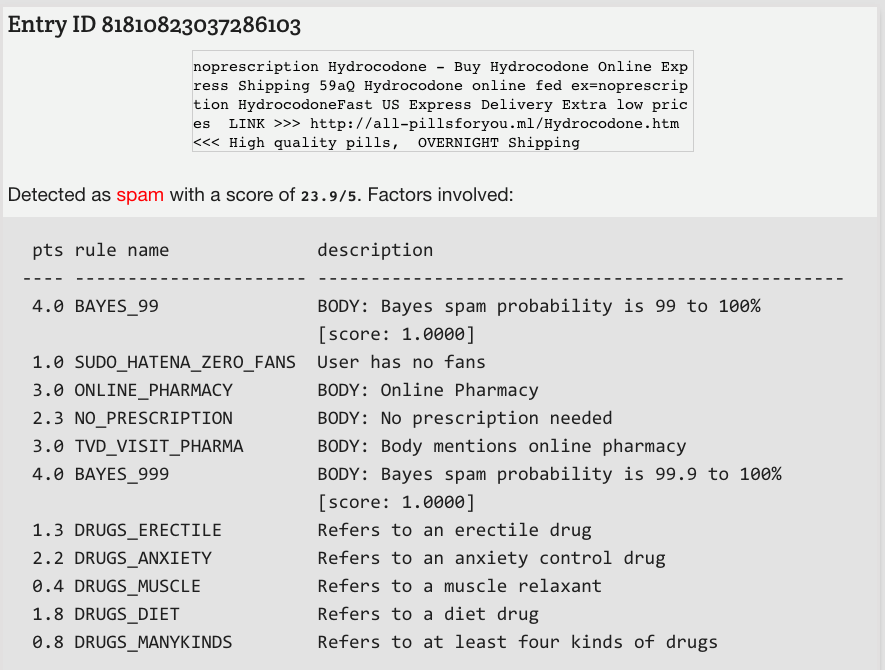
最近の例です(最近はドラッグ関連のスパムが増えており、このような内容のフィルタリングは比較的簡単です)。
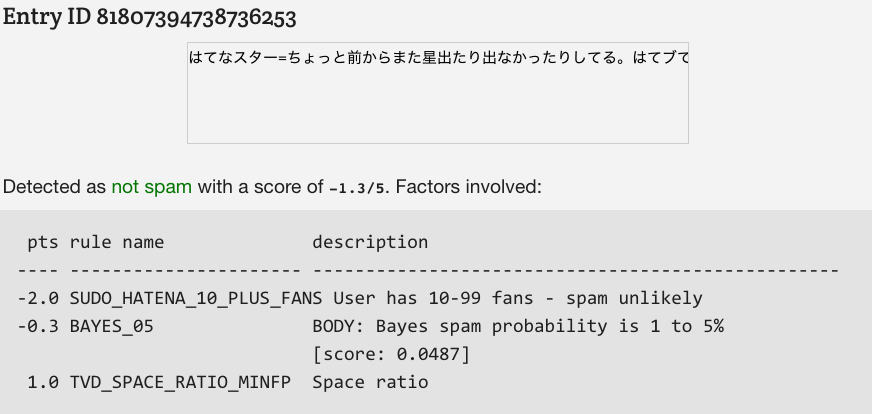
正当なメッセージの例です。
API
はてなハイクスパム対策のAPIを提供しています。
スパムのフィルタリングに最もよく使用するものは、最近のスコアのAPIです。
https://haikuantispam.lightni.ng/api/recent_scores.json
これにより、最近投稿しているはてなIDと、そのスコアが示されます。スコアが5を超えるとスパムと見なされます。
こちらは最近のキーワードのAPIです。
https://haikuantispam.lightni.ng/api/recent_keywords.json
ハイクのキーワードの性質上、特定のキーワードに善悪のラベルを付けることは簡単ではありません。ここでのスコアは、各キーワードに対する投稿の最近のスコアの平均を使用して得られます。それでも、ページの右側にあるキーワードリストを更新することは有益です。
ユーザースクリプト
id:noromanba氏が、最近のスコアのAPIを利用して、はてなハイクをブラウズするときにスパムをフィルタリングする優れたユーザースクリプトを開発されました。インストールすることをお勧めします。
(Tampermonkey、ViolentmonkeyまたはGreasemonkeyで使用できます。私個人では、すべての最新のブラウザーとの互換性を備えた、Tampermonkeyを使用しています)。
ページの上部に、スクリプトへのリンクがあります。

次のリンクから直接アクセスできます。
Slack用のリッチコンテンツタグ
この機能の用途は限られていますが、ハイクスパム対策のリンクを付けてユーザーをはてなに報告するたびに、Slackbotからのヒットが発生している(つまりはてなでSlackが使用されている)ことに気付きました。このため、ハイクスパム対策によって分類されるユーザーの概要を示すタグを追加しました。

今後
さまざまな自分のプロジェクトの管理が多忙にしていますが、ハイクスパム対策の保守と改善は必ず続けます。私の真の願いは、はてなと協力して、同社のサービスのための正確でスケーラブルなスパム検出システムを開発すること、あるいは、最小限、その実現方法のアイデアと例を提供することです。
はてなハイクスパム対策に対しては、次のことを近日中に更新するつもりです。
- 分類に使用する投稿の格納方法
- データベース: 現在は、ポータブルであるためSQLiteを使用していますが、時間の経過に伴い、適切にスケーリングできなくなる可能性があります。ハイクスパム対策にはすでに時折タイムラグが見られます(APIでは結果をキャッシュし、ユーザーのリクエストとは独立して更新を実行するため、タイムラグは発生しません)。アプリケーションをMySQLに移行することを計画しています。
- ハイクスパム対策バックエンドとサイトマージ: 現在、GitHub上のコードはバックエンド向けのもののみとなり、サイトのフロントエンド向けのものはありません。MySQLへの移行が完了し、サービスに関与するファイルへの直接アクセスや直接のパスを除去したら、Webサイトの部分もGitHubに配置することを計画しています。
Thank you to id:PlumAdmin for the translation of the original article. I am very grateful.
読者になる,くださいか?